In addition to physical desktops and laptops, the college offers virtual machines/hosted desktops through our private cloud.
Jump to:
About Virtual Machines/Hosted Desktops
What is a virtual machine?
A virtual machine is a Windows computer, just like a dedicated laptop or desktop, but it is running on a shared hardware platform. This “computer” is actually located in the college data center, hosted on a cluster of servers.
What benefits come from using a virtual machine?
When you access your virtual machine, you are technically connecting to a computer that is internal to the college network. The enhanced security measures in place on the virtual machine offer better protection from malware and other security risks. Virtual machines are expendable and facilitate quick recovery if there is any issue in the computer. If there is a problem, it can be replaced quickly without an office visit from a technician. There is no physical PC hardware to fail in the office. The biggest benefit is Access Anywhere!
What is Access Anywhere?
As long as you have a device with access to the internet and that is: capable of running a web browser; a thin client; or a PC with the VMWare Horizon Client installed, you can access your virtual machine. Excellent performance is available with the lowest cost cable and DSL options as well as MiFi hotspots. There is no need to worry about security when connecting from an open wifi network like that provided at a conference, hotel, or other convenience location, as the connection back to the college is fully encrypted and secured using SSL.
Why does the college use virtual desktops?
There are several reasons why virtual desktops are used at VWCC. Management of the large group of computers needed by the campus community is more efficient using the virtual desktop system. Pooled resources are available to the user community as a whole, facilitating sharing of resources. Improved security, faster problem resolution, energy efficiency, flexibility and audit compliance are all factors in the decision to use virtual systems. Office relocations are able to be done without moving computer equipment. The ability to access the hosted desktop from anywhere on or off campus allows end user mobility with minimal expenditure of resources. Another key benefit is that the virtual systems have a small carbon footprint and generate minimal eWaste demonstrating the college’s regard for the environment. Since there is no actual data residing on the thin client and it is not functional without connection to the college network, theft and data security are not concerns. Access to multiple virtual machines can be provided to facilitate transition from one version of Windows to another.
What is the benefit of connecting at home?
By connecting to your virtual machine from home, you will have access to all resources internal to VWCC. The desktop is the same as the one you use every day. All applications, documents, and your recent work history are all in that machine. You can simply disconnect at work, leaving the machine where you were working, go home, and resume at the same place where you left off. Disconnect from home and when you return to work, the machine is right where you left off. For those with older, lower powered computers, remote access to a powerful virtual machine eliminates the need to upgrade. The browser or Horizon Client provides remote control over the virtual machine in the same manner as the thin client.
Note: This option is only available for exempt personnel unless specifically approved through your supervisor and Human Resources.
How much disk space does a virtual machine have?
Virtual machines are configured with 60GB of hard drive space for the C: drive. This can be increased if needed. Note: Best practice is to store important data on network drives or in My Documents, which is redirected to a network location. Storing data on the local drive creates multiple problems and is not supported.
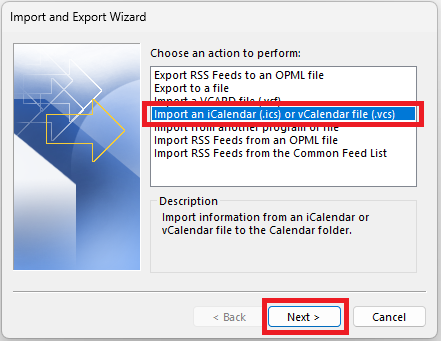
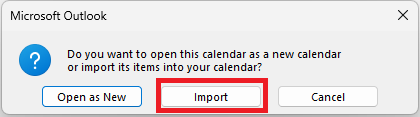
How to Access Your Virtual Machine
Your virtual machine can be accessed from any thin client on campus, a VWCC desktop or laptop PC, from home via web browser on another computer, or by using the VMWare Horizon Client on another computer (even a Mac!). The virtual PC actually works like an application when it is accessed from another computer, and can be minimized like any other application. It can also be accessed from an Android tablet, iPad, or phone (though it may be cumbersome due to the screen size). Special keys and tools allow replication of the mouse on devices that don’t have one.
How to Access Your Virtual Desktop on campus
How to Access Your Virtual Desktop from Off-Campus
What is a thin client?
A thin client is a device that provides a remote connection to the virtual desktop. The device is designed to communicate with the virtual computer using specialized protocols that make the thin client appear to be a fully functional computer. In the vast majority of cases, thin clients meet the needs of information work tasks, saving the college money and reducing energy costs as well as eWaste.
Is a thin client slower than a regular computer?
A thin client is not a computer, but a device that remotely accesses the virtual machine so speed is not comparable. A standard template is used to build a machine for a typical knowledge worker using Office applications, web browsing, and email. Performance problems are not typical and should be reported to the Help Desk for analysis. In some cases, the virtual machine needs to be given more resources to match the applications in use by the system user.
Using & Troubleshooting Your Virtual Machine
On Mondays, my virtual machine always has to boot up. Why?
Each weekend, all virtual machines are shut down and restarted. This sets them up to get updates and forces a complete login process, which is used to deliver configuration changes.
Why does it take a long time for a virtual machine to boot up?
The virtual desktop boots like any other desktop. The typical boot time is under 2 minutes for Windows 7 machines. Physical machines have a comparable boot time. The virtual desktop does not need to be shut down every day. Powering all the virtual machines in the system all the time takes resources, so the option to boot them up was chosen to conserve power when the machines are not in use.
Note: To avoid having to boot up each morning, simply disconnect rather than shut down at the end of the day.
Can I use a USB stick on a virtual machine?
Yes, you can. On a thin client this is natively supported as it would be on any PC. Virtual machines will connect to the USB stick or any USB device. Note: If you are accessing a virtual machine from home, formatting the stick with the FAT32 filesystem will make it work faster.
Are the drive mappings the same on a virtual PC, laptop, and full desktop?
Drives are mapped based on user id and department as well as participation in special collaboration groups. Open Windows Explorer or My Computer and review your drive mappings. You will see your normal drive configuration as well as additional drives that appear with a number in the description (the ID number of your campus workstation, or some other nomenclature if accessing from a home PC). The local computer name is attached to the drive description to show you where the drive resides. As you look at the drives and explore the content, you will be able to see the additional resources that are available.
What is the recommended way to end a virtual session?
- Disconnect and log off each day — this closes all files in an orderly fashion.
- If you use the virtual machine frequently (daily Monday to Thursday) you may also disconnect. It will be ready to go when you sign back in without a reboot. It is recommended that you save files in any open application such as Excel or Word to make sure you saved your work.
- On Friday, disconnect and log off or shut down.
Can I use my thin client to charge my phone?
Technically, yes. Practically, this is not recommended. The thin client is a computing device designed to consume a low amount of power. It was not designed to be a phone charger. Charging high power consumption devices or using a USB hub to plug multiple devices into the unit will create an under voltage problem on the thin client.
I have used a dual monitor configuration before, can I use 2 monitors on a thin client?
Yes, you can. Dual monitors are available for thin clients.
When I do a CTRL-ALT-DEL while in the hosted desktop connected from a PC or laptop, it prompts me to use CTRL-ALT-INS instead. Why?
This only happens when you use the VMWare Horizon Client on a PC to access your virtual machine. This does not happen on a thin client. The virtual machine uses CTRL-ALT-INS instead of CTRL-ALT-DEL to distinguish between what this key combination does in each computer. It is cumbersome and a bit confusing, but using the incorrect combination results in a prompt telling the user what to do, so there is no problem if the wrong sequence is entered.
If I have question about using a virtual machine or have an issue with my present configuration, what do I do?
Open a work request with IET through the Help Desk. An analyst will be happy to work with you to obtain a solution.